Building AML monitoring workflows on verified bank data?
Finexer gives UK platforms FCA-authorised AIS access – structured, continuous, audit-ready.
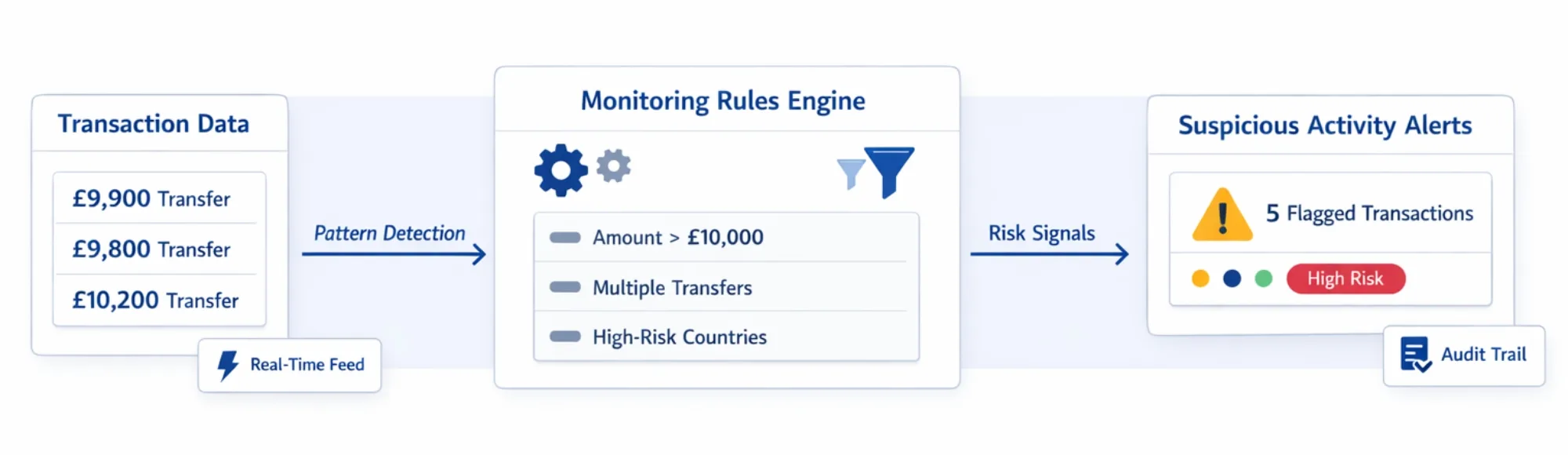
A transaction monitoring system does not detect suspicious activity on its own. It detects what its rules tell it to detect.
This distinction matters more than most platforms acknowledge during compliance infrastructure design. The system is the mechanism. The transaction monitoring rules are the compliance logic. Without well-defined rules running on reliable data, the system produces either nothing useful or an unmanageable volume of false positives.
In my experience working with LawTech platforms, compliance SaaS providers, and regulated fintech teams, the rule definition layer is where most monitoring implementations either succeed or fail. Teams invest in monitoring infrastructure and neglect the rule design that determines what that infrastructure actually catches.
This blog explains what transaction monitoring rules are, which rule types matter for AML compliance, why rules fail without proper data, and how Finexer’s verified bank transaction data enables platforms to apply those rules reliably.
TL;DR
Transaction monitoring rules are predefined conditions that compliance systems use to flag suspicious financial activity. AML transaction monitoring rules cover thresholds, behavioural patterns, frequency detection, and structuring indicators. These rules are only as reliable as the bank transaction data they run on – which is where Finexer’s FCA-authorised AIS infrastructure provides the verified data foundation that monitoring logic requires.
Key Takeaways
What are transaction monitoring rules?
Transaction monitoring rules are predefined conditions used to identify suspicious financial activity based on transaction behaviour, frequency, and value. They define what a monitoring system flags for compliance review – without rules, no alerts are generated regardless of what activity occurs.
What are AML transaction monitoring rules?
AML transaction monitoring rules are compliance-driven conditions specifically designed to detect potential money laundering, structuring, or suspicious financial behaviour. They operate against bank transaction data and produce alerts that compliance teams investigate and report where required.
Why do transaction monitoring rules fail without verified bank data?
Rules applied to incomplete, manually collected, or unverified transaction data produce unreliable outputs. Structuring patterns that span multiple accounts are invisible if only one account is connected. Threshold rules misfire when transaction data is delayed or formatted inconsistently across sources.
Which platforms need to define AML transaction monitoring rules?
LawTech platforms conduct source-of-funds checks, compliance SaaS providers building monitoring engines, regulated fintech platforms under MLR 2017 obligations, and any platform that monitors client financial activity for AML purposes.
Where does Finexer fit in transaction monitoring rule workflows?
Finexer provides the verified bank transaction data that transaction monitoring rules run on. Platforms define their own AML logic – Finexer provides the structured, continuous, bank-authenticated data feed that makes those rules operationally reliable.
What Are Transaction Monitoring Rules?

Transaction monitoring rules are the decision layer of any AML monitoring system. They define the conditions under which a transaction or pattern of transactions triggers a compliance alert.
Without transaction monitoring rules, a monitoring system has no detection logic. It receives transaction data and does nothing with it. The rules are what transform raw financial data into compliance-relevant signals.
“Transaction monitoring rules are the compliance logic that sits between raw financial data and a Suspicious Activity Report. The quality of that logic determines the quality of the compliance outcome.” – Paul, Finexer
For UK regulated platforms operating under the Money Laundering Regulations 2017, transaction monitoring rules must be designed to detect the financial patterns that indicate money laundering risk – not just capture high-value transactions arbitrarily.
The UK Government’s transaction monitoring privacy notice outlines the regulatory framework within which transaction monitoring obligations operate.
What Types of AML Transaction Monitoring Rules Do Platforms Use?
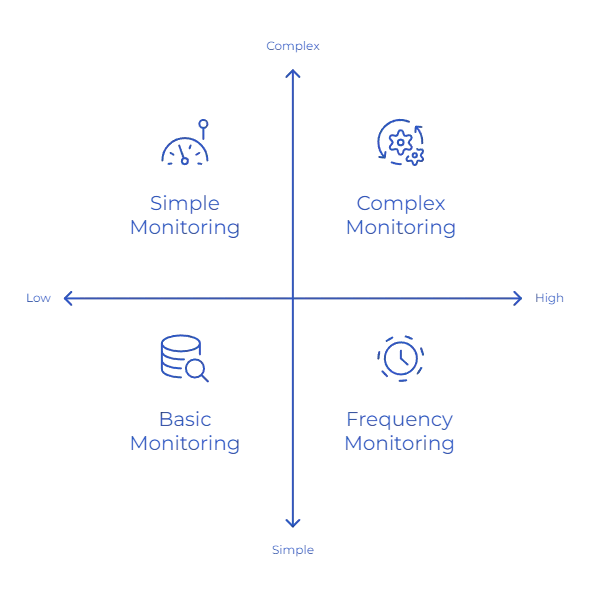
Threshold-Based Rules
The most straightforward transaction monitoring rules operate on value thresholds. Transactions above a defined amount trigger review. These rules are easy to implement but produce high false-positive rates when applied without contextual calibration.
Effective threshold rules account for client profile and expected transaction behaviour – a £50,000 transaction from a property conveyancing client carries different risk signals than the same amount from an account with no prior high-value activity.
Frequency Rules
Frequency-based transaction monitoring rules flag unusual transaction volume within a defined time window. Multiple transactions in rapid succession, repeated transfers to the same counterparty, or sudden spikes in transaction count relative to account history all trigger frequency alerts.
These rules are particularly relevant for detecting account takeover patterns and payment layering in AML workflows.
Behavioural Rules
Behavioural transaction monitoring rules compare current financial activity against established baseline patterns for the same account. A client who has never made international transfers and suddenly initiates several in a week triggers a behavioural deviation alert.
Behavioural rules require transaction history depth to establish the baseline. This is one reason why AML transaction monitoring rules fail when platforms only access 30-90 days of transaction data.
Pattern-Based Rules
Pattern-based AML transaction monitoring rules detect structuring – the practice of splitting transactions to stay below reporting thresholds. Multiple transactions just below a threshold value, spread across short time intervals, are a structuring indicator that single-transaction threshold rules miss entirely.
Detecting structuring requires multi-transaction pattern analysis across a sufficient time window and across multiple accounts where possible.
Why Do Transaction Monitoring Rules Fail Without Proper Data?
The most precisely calibrated transaction monitoring rules produce unreliable outputs when the underlying data is incomplete, delayed, or unverified.
I see three consistent data failure modes in platforms that have invested in monitoring rule logic but not in data quality:
Incomplete account coverage. Structuring patterns that span multiple accounts are invisible when the monitoring system only sees one. A client moving funds between three accounts to avoid detection is undetectable if only the primary current account is connected.
Data latency. Frequency rules that require transaction data within a 24-hour window cannot operate correctly on weekly batch imports. By the time the data arrives, the activity window has passed.
Unverified data sources. Rules applied to manually submitted bank statements carry the risk of the statement itself being incomplete or altered. A client who excludes certain transactions from a manually uploaded PDF creates blind spots in monitoring rule coverage that the system cannot detect.
Automated transaction monitoring using bank APIs covers how automation addresses the data latency problem in monitoring workflows.
How Should Platforms Evaluate Data Infrastructure for Transaction Monitoring Rules?
| Data Requirement | Which Rule Type Depends on It | What to Look For |
|---|---|---|
| Transaction History Depth | Behavioural rules require baseline history; pattern rules need extended lookback | Up to 7 years transaction history; configurable lookback periods |
| Real-Time Transaction Feed | Frequency rules and structuring detection require current transaction data | Real-time webhooks; continuous transaction feeds; event-driven delivery |
| Multi-Account Coverage | Structuring and layering detection requires cross-account visibility | Multi-account AIS access; 99% UK bank coverage; cross-bank aggregation |
| Structured Data Output | All rule types require consistently formatted transaction records | Structured JSON; merchant IDs; counterparty details; category codes |
| Verified Data Source | AML rule outputs are only defensible if the underlying data is bank-verified | FCA-authorised AIS; consent-based access; bank-authenticated transaction records |
| Audit Trail | SAR preparation and regulatory review require data access records | Consent logs; access timestamps; data provenance records per retrieval |
How Does Finexer Enable Transaction Monitoring Rule Workflows?
Finexer provides FCA-authorised AIS infrastructure delivering the verified bank transaction data that transaction monitoring rules run on. Platforms define their own AML logic – Finexer provides the structured, continuous data feed that makes that logic operationally reliable.
What Finexer’s AIS provides for transaction monitoring rule workflows:
- Structured bank transaction data from 99% of UK bank accounts
- Real-time webhooks delivering transaction events as they occur
- Transaction history up to 7 years for behavioural baseline and pattern lookback
- Multi-account data access from a single consent-based API connection
- Counterparty details and merchant identifiers per transaction
- FCA-compliant consent flows with granular permissions and instant revocation
- Usage-based pricing
Transaction monitoring solutions for UK platforms cover the broader monitoring infrastructure layer in detail.
Real-time transaction monitoring for fintech platforms cover the real-time data delivery requirements for frequency and behavioural rules.
What I Feel
The compliance teams I work with that build effective transaction monitoring rule systems share one characteristic – they design the data layer before they design the rules.
It seems backwards to most teams. The instinct is to define the rules first and then figure out the data. But transaction monitoring rules have specific data dependencies. Behavioural rules need history depth. Frequency rules need real-time feeds. Structuring detection needs multi-account coverage.
Building AML transaction monitoring rules on a data foundation that cannot support those dependencies produces a monitoring system that looks complete but has structural detection gaps. The rules exist. The alerts are generated. But the underlying data is missing the transactions that matter most.
Common Use Cases

LawTech Platforms
LawTech platforms – including conveyancing practices and insolvency firms – use Finexer’s AIS to access verified client bank transaction history for source-of-funds monitoring. Transaction monitoring rules applied to continuous bank data feeds detect unusual financial patterns during case lifecycle – supporting MLR 2017 ongoing monitoring obligations with bank-authenticated evidence rather than periodically submitted documents.
Compliance SaaS Platforms
Compliance SaaS providers embed Finexer’s AIS as the verified data layer beneath their AML transaction monitoring rule engines. Structured transaction data with counterparty details, category codes, and multi-account coverage gives rule logic the data quality it needs to produce reliable alerts – reducing false positives from incomplete or inconsistently formatted data sources.
Regulated Fintech Platforms
Regulated fintech platforms operating under MLR 2017 use Finexer’s AIS to maintain continuous transaction visibility for monitoring rule application. Real-time webhooks ensure frequency rules operate on current data – not on delayed imports that create detection windows between data collection cycles.
Accounting & ERP Platforms
Accounting platforms with AML obligations use AIS transaction data to apply transaction monitoring rules against client financial activity. Behavioural rule baselines are established from transaction history – flagging unusual activity relative to established client financial patterns rather than applying generic thresholds that produce high false-positive rates for legitimate business activity.
Insurtech Platforms
Insurtech platforms use verified bank transaction data to apply AML transaction monitoring rules during claims processing and client onboarding. Structured transaction feeds enable pattern-based rule detection across the full transaction history – identifying financial behaviour anomalies that static document review would miss entirely.
What are transaction monitoring rules in AML compliance?
Transaction monitoring rules are predefined conditions that compliance systems use to flag suspicious financial activity. AML transaction monitoring rules cover value thresholds, transaction frequency, behavioural deviations, and structuring patterns – each designed to detect specific money laundering indicators within bank transaction data.
Why do AML transaction monitoring rules depend on verified bank data?
AML transaction monitoring rules produce reliable outputs only when applied to complete, current, bank-verified transaction data. Manually submitted statements create coverage gaps, latency, and verification risks that undermine rule accuracy – leading to missed suspicious activity and false positives that consume compliance team capacity.
Is Finexer suitable for platforms building transaction monitoring rule systems?
Yes. Finexer is FCA-authorised and provides AIS infrastructure covering 99% of UK banks – delivering structured bank transaction data with counterparty details, category codes, and up to 7 years of transaction history. Platforms apply their own AML transaction monitoring rules against Finexer’s verified, continuous bank data feeds.
Apply transaction monitoring rules on verified bank data that compliance teams can defend.