Consent-driven. Audit-ready. FCA-authorised.
Secure financial data access infrastructure for UK fintech compliance teams.
Secure financial data access in fintech refers to the ability to retrieve and use customer financial data through APIs while maintaining strict security, consent, and regulatory compliance standards.
In the UK, this means operating under UK GDPR, the Data Protection Act 2018, FCA supervisory requirements, and the Open Banking security framework – all simultaneously.
The security layer is not just technical. It is regulatory, operational, and audit-facing.
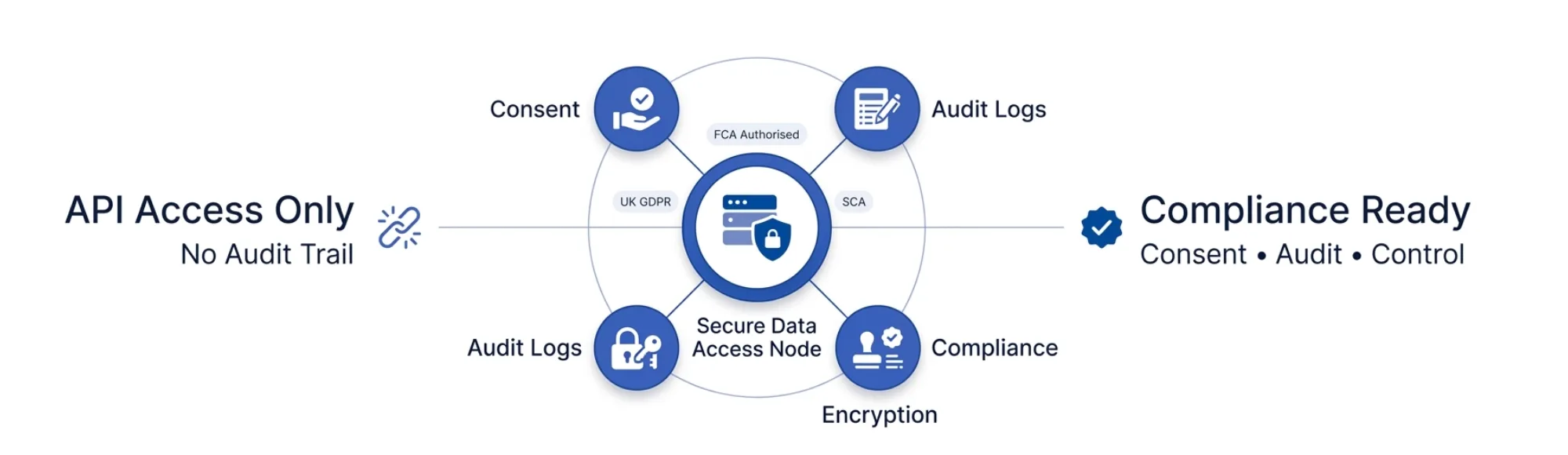
In my work with compliance and risk teams at Finexer, the gap in secure financial data access is rarely in encryption. It is almost always in consent traceability, audit depth, and whether the data access infrastructure can demonstrate compliance to a regulator – not just to a developer.
TL;DR
Secure financial data access in UK fintech operates under UK GDPR, FCA oversight, and PSD2/Open Banking standards. It requires SCA at authentication, encrypted data in transit and at rest, consent logs per retrieval, and audit trails per access event. The platforms that get this right treat security not as an API feature but as an infrastructure requirement – covering authentication, authorisation, consent, logging, and data security in financial services reporting from day one.
Key Takeaways
What does secure financial data access require in the UK?
It requires five layers working together:
- Authentication – SCA at the bank level, not just API key validation
- Authorisation – consent per user, per data scope, per retrieval
- Encryption – data encrypted in transit and at rest
- Audit logging – per-access records with timestamps, user identity, and data scope
- Regulatory compliance – FCA authorisation, UK GDPR alignment, and DSAR-readiness
What is the difference between API security and compliance-ready data access?
API security prevents unauthorised access. Compliance-ready data access proves that authorised access was legitimate, consent-based, and auditable. A platform can have strong API security and still fail a compliance review if it cannot produce per-retrieval consent logs and access timestamps on request.
What are the key UK regulations governing financial data access?
Three primary frameworks apply:
- UK GDPR / Data Protection Act 2018 – purpose limitation, data minimisation, 72-hour breach notification
- FCA supervisory requirements – operational resilience, third-party risk management (SS6/24, PS16/24)
- Open Banking / PSD2 – SCA, consent-based access, API security standards
Why do compliance teams need audit trails beyond standard API logs?
Regulators, auditors, and DSAR requests require evidence of who accessed what data, under which consent, and at what time. Standard API logs record requests. Compliance audit trails record consent provenance, access scope, data subject identity, and retrieval purpose – each linked to a specific consent event.
What Does Secure Financial Data Access Actually Require?
What Are the Security Standards for Financial Data Access in the UK?
The UK’s secure financial data access framework combines regulatory requirements with technical standards:
| Requirement | Framework | What It Means in Practice |
|---|---|---|
| Strong Customer Authentication | PSD2 / Open Banking | Two-factor authentication at the bank before data is released |
| Consent-based access | UK GDPR / Open Banking | Explicit user consent per data scope, with withdrawal rights |
| Data encryption | FCA / UK GDPR | Encrypted in transit (TLS) and at rest for all financial data |
| Audit logging | FCA / UK GDPR Article 5 | Per-retrieval records with timestamp, scope, and user identity |
| Breach notification | UK GDPR Article 33 | 72-hour notification to ICO for reportable personal data breaches |
| Third-party risk management | FCA SS6/24 | Documented vendor assessment for any provider handling financial data |
Financial data protection for UK regulated platforms covers how UK GDPR and FCA requirements apply specifically to platforms accessing financial data through Open Banking APIs.
“Secure financial data access is not a checkbox. It is a continuous operational posture. Consent logs that cannot be produced on request, audit trails that only cover API calls, and data access that is encrypted but not traceable – these are the gaps that appear in regulatory reviews, not security audits.” – Paul, Finexer
Where Does Secure Financial Data Access Break Down?
What Are the Real Gaps in Financial Data Security for Fintech Platforms?
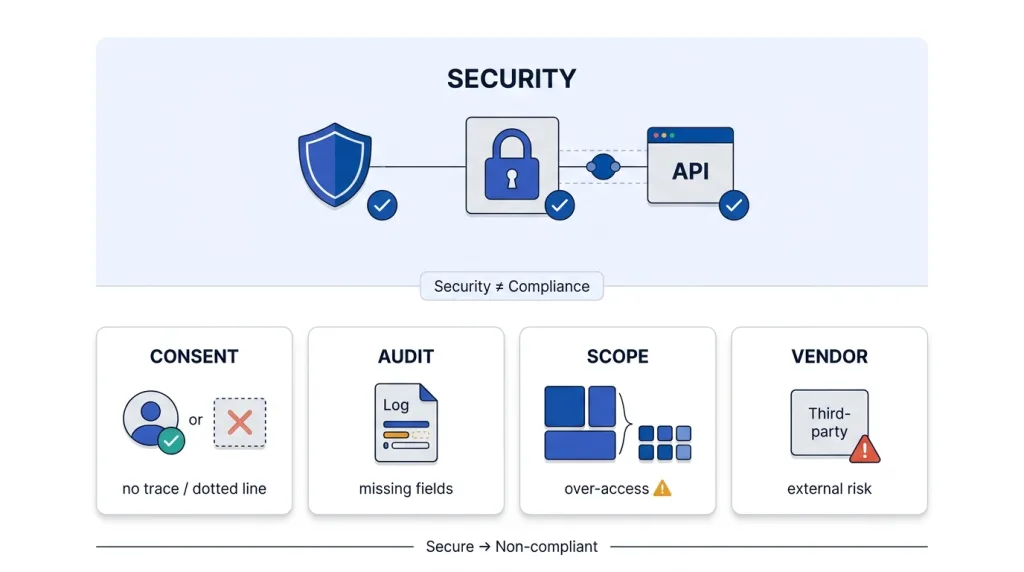
Most fintech platforms address the technical security layer correctly. Encryption is in place. API keys are managed. Authentication is handled. The gaps appear in the compliance and operational layer:
Consent traceability:
- User gives consent via a provider flow
- The platform receives data but holds no per-retrieval consent record
- If a DSAR or regulatory review requests consent provenance, the platform cannot produce it
Audit trail depth:
- Standard API logs record request and response
- They do not record which user consented, under which data scope, or for which purpose
- Audit-ready financial data access requires logs at the consent level, not the API level
Data minimisation gaps:
- Platforms accessing broader data scopes than required for the stated purpose
- UK GDPR Article 5 requires data collected is limited to what is necessary
- Accessing 12 months of transaction history when 3 months satisfies the use case = non-compliant
Third-party vendor risk:
- FCA SS6/24 requires documented risk assessment of any third party handling regulated data
- Choosing an unregistered or non-FCA-authorised provider creates direct regulatory exposure
- The platform inherits the compliance gap of its data access provider
Bank integration API for secure financial data access covers how integration architecture decisions at the API layer affect compliance posture for regulated UK platforms.
How to Evaluate Secure Financial Data Access Providers
What Criteria Predict Compliance Readiness in Production?
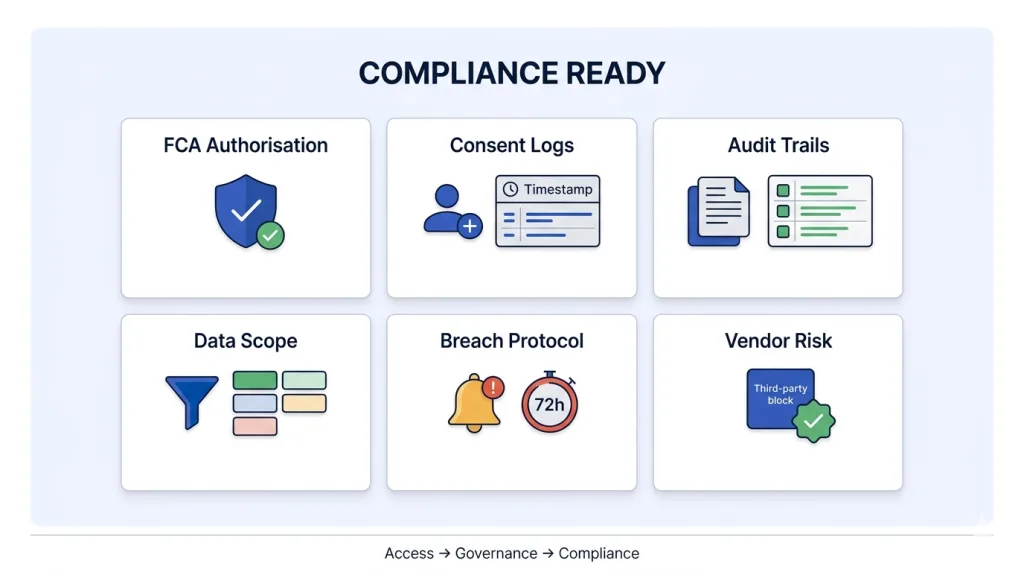
Evaluating secure financial data access providers on sandbox security and API documentation reveals technical capability. For compliance teams responsible for data security in financial services, these criteria reveal compliance readiness:
- FCA authorisation – is the provider registered as an AISP/PISP with the FCA? An unregistered provider creates direct regulatory exposure
- Consent log depth – does the provider deliver per-retrieval consent records with timestamps, user identity, and data scope?
- Audit trail format – are access logs structured for regulatory review, or are they standard API logs requiring manual interpretation?
- Data minimisation controls – can the platform configure data scope per consent to collect only what is necessary for the stated purpose?
- Breach notification protocol – does the provider have a documented ICO notification process within the 72-hour UK GDPR requirement?
- Third-party risk documentation – can the provider supply the security and compliance documentation required for FCA SS6/24 vendor assessments?
How Does Finexer Support Secure Financial Data Access?
What Does Finexer’s AIS Provide for Compliance-Ready Data Access?
For platforms that need both secure access and compliance-ready workflows, Finexer’s FCA-authorised AIS provides consent-driven financial data access with structured audit trails and full regulatory alignment in a single integration.
Finexer AIS API – real-time bank data for UK platforms covers how Finexer’s AIS architecture delivers structured, consent-based bank data with per-retrieval logging for compliance workflows.
Finexer’s AIS provides:
- Consent logs per retrieval – each data access event logged with timestamp, user identity, and data scope
- FCA-authorised infrastructure – registered AISP under FRN925695, meeting FCA operational resilience and third-party risk requirements
- SCA at bank level – authentication handled directly within the user’s bank app, not at the platform layer
- Structured JSON – consistent, auditable data format across almost all major UK banks
- UK GDPR-aligned consent flows – explicit per-user, per-scope consent with withdrawal rights
- Up to 7 years of transaction history – configurable access depth to support data minimisation requirements
- Multi-account access in one consent flow – full financial picture per client with single consent event
- Usage-based pricing, white-label consent flows, deploys 2-3x faster than market alternatives
Finexer Data product page covers the full AIS capability set and compliance documentation available for vendor assessment purposes.
“VirtualSignature-ID integrated Finexer to streamline onboarding and Source of Funds workflows. David Kern, CEO, said: ‘Finexer is easy to work with and flexible in their approach, providing the bespoke services we require alongside a viable commercial package. Finexer has proven to be more than a provider – they’re a trusted partner who understands our vision and helps us achieve it.’”
What I Feel
Compliance teams evaluate providers on security certifications. Regulators review consent records.
These are different tests.
A provider can hold ISO 27001 and still fail a DSAR request because consent logs were never created at the retrieval level.
“In regulatory reviews, the question is never just ‘is the data encrypted?’ It is ‘can you show me the consent record for this retrieval, the timestamp, and the data scope?’ Most platforms cannot.” – Paul, Finexer
Secure financial data access for a UK fintech means the data arrives encrypted, the consent is logged, the audit trail is complete, and the provider is FCA-authorised. All four. Not three.
Common Use Cases
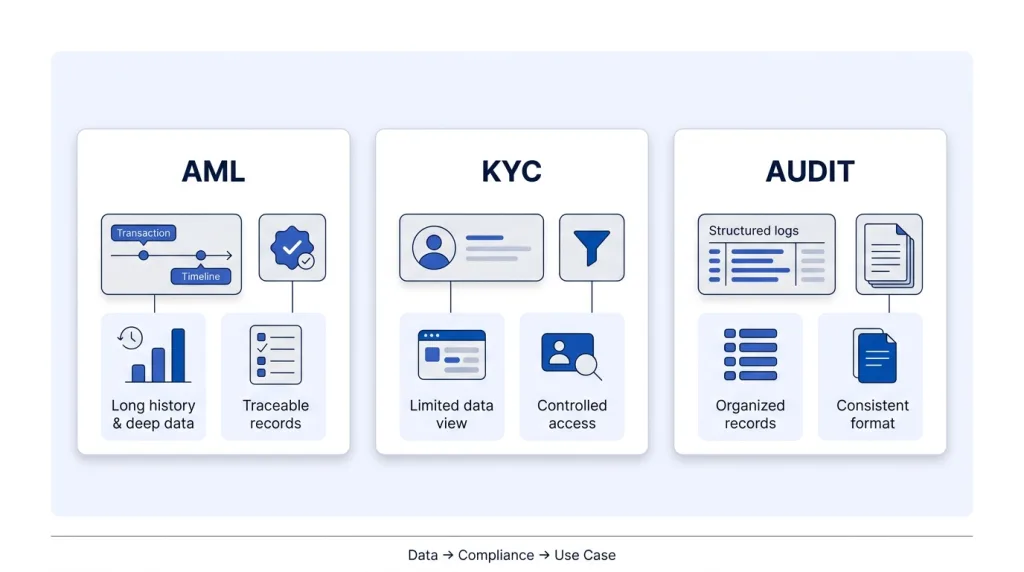
AML and Source of Funds Platforms
AML workflows require demonstrable, consent-based access to financial history with a clear audit trail per retrieval. Finexer’s AIS delivers:
- Up to 7 years of transaction history per account
- Consent logs and access timestamps per retrieval
- FCA-authorised access under structured UK Open Banking standards
Onboarding and KYC Platforms
KYC and identity platforms accessing financial data during onboarding must demonstrate data minimisation – collecting only what the stated purpose requires. Finexer’s configurable consent scopes and per-retrieval logs support both FCA and UK GDPR compliance documentation.
Compliance and Audit Platforms
Platforms providing financial audit and compliance workflows need structured, consistently formatted data with an auditable access history. Finexer’s structured JSON and consent logs per retrieval provide the data and documentation layer that audit workflows require.
What is secure financial data access in fintech?
Secure financial data access in fintech is the ability to retrieve customer financial data through FCA-authorised APIs with SCA, consent logging, encryption, and audit trails. In the UK, it operates under UK GDPR, the Data Protection Act 2018, and FCA supervisory requirements. Security covers both technical protection and compliance traceability.
What does data security in financial services require beyond encryption?
Data security in financial services requires consent logs per access event, audit trails per data retrieval, data minimisation controls limiting access to what the stated purpose requires, and documented third-party risk assessment under FCA SS6/24. Encryption protects data in transit and at rest, but compliance requires demonstrating that every access was consented, scoped, and traceable.
How do consent logs support compliance in financial data access?
Consent logs record who authorised data access, under which scope, and at what time – per retrieval event. They are required for DSAR responses under UK GDPR, regulatory reviews under FCA oversight, and audit trails for AML and Source of Funds workflows. Standard API logs do not substitute for consent-level records.
Build compliant financial data access on FCA-authorised infrastructure with full audit trails.