Consent-based bank data access. Encrypted transmission. Structured, verifiable financial records.
Open Banking AIS infrastructure for accounting SaaS, lawtech, compliance platforms, and financial operations tools.
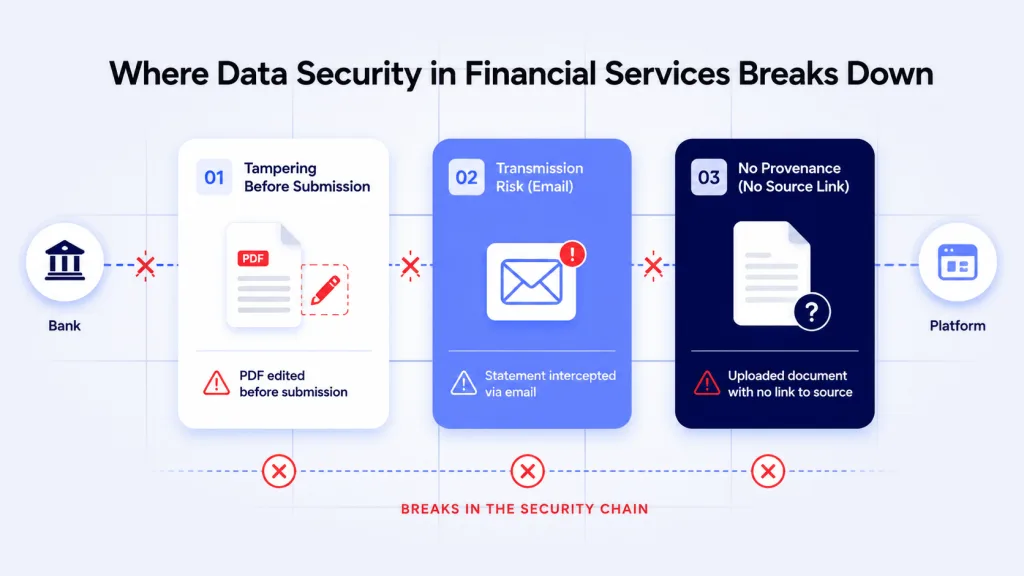
Data security in financial services breaks down long before the database. Most platforms are securing data that arrived via email, a client-uploaded PDF, or a manually downloaded statement – none of which have any verifiable chain of custody to the bank that issued them.
The average data breach in financial services costs $5.9 million, the second highest of any industry and 37% above the global average (IBM Cost of a Data Breach Report, 2025). Most of those incidents begin not in the database, but in the data collection workflow.
I work with compliance leads, product teams, and finance ops managers who have invested in encryption, access controls, and audit logs. The storage infrastructure is solid. This blog covers the step before it – how data gets there, and why data security in financial services so often fails at that earlier point.
TL;DR
Data security in financial services fails at the collection step, not the storage step. A PDF can be altered before it reaches the platform – no encryption policy prevents this. Open Banking AIS retrieves bank data directly from the source, consent-based and bank-authenticated, removing the document fraud risk that manual statements cannot eliminate.
Key Takeaways
Is data security an FCA rule in the UK?
Yes. The FCA requires regulated firms to maintain secure systems and controls for customer data under SYSC 8 and the FCA Handbook. This includes data integrity, access controls, and breach notification. Under UK GDPR, firms must report personal data breaches within 72 hours. Open Banking AIS access also falls under Payment Services Regulations 2017.
Why is manually fetching bank statements a security risk?
PDF bank statements can be edited before submission using widely available tools. Client-submitted documents carry no cryptographic proof they were unaltered between the bank and the platform. Email transmission introduces interception risk. Manual uploads create no audit trail connecting the document to the bank that issued it.
How does Open Banking improve data security in financial services?
Open Banking AIS retrieves financial data directly from the bank with the user’s consent. Data travels bank-to-platform via encrypted API – no intermediary, no manual handling. The platform receives bank-verified records. This is the core improvement to data security in financial services – removing the document fraud vector entirely, and eliminating the need to fetch bank statements manually.
What UK regulations govern financial data access?
Data security in financial services in the UK is governed by UK GDPR, the Data Protection Act 2018, and Payment Services Regulations 2017. The Data (Use and Access) Act 2025 updates data sharing obligations. The Cyber Security and Resilience Bill adds operational resilience requirements. FCA-authorised providers must meet the PRA’s PS7/26 framework published March 2026.
Where Does Data Security in Financial Services Actually Break Down?
Why Data Collection Is the Weakest Point
Ask most compliance teams where data security in financial services fails and they will point to the storage layer. The real answer is earlier. Secure storage is table stakes. Most platforms encrypt data at rest, restrict access by role, and maintain audit logs of every database query.
These controls are necessary. But data security in financial services requires more than this – because these controls only protect data that has already arrived.
The gap is earlier – in how that data gets there.
Accounting SaaS, lawtech firms, and compliance platforms regularly ask clients to submit bank statements for Source of Funds checks, affordability assessments, and AML due diligence. The platform’s security controls activate once the document lands. But by then, it may already have been altered.
There are three ways this fails in practice.
- Tampering before submission. PDF editing is trivial. A client can alter transaction amounts, remove entries, or change dates using free tools before uploading. The platform receives a document that looks authentic but carries no proof of integrity. No storage encryption prevents this – the document was compromised before it entered the system.
- Interception in transit. Statements sent by email pass through servers the platform does not control. Email is not end-to-end encrypted by default. This is a routine data handling gap that creates real data security exposure in financial services – and it is entirely preventable.
- No provenance to the source. This is a fundamental data security gap in financial services. A manually uploaded statement creates an internal record of when it arrived. It creates no record connecting the document to the bank that produced it. In a regulatory review, that gap in chain of custody matters.
“The data integrity question in financial compliance is not just about storage security. It is about whether the platform can demonstrate that the records it relied on came directly from the bank, unaltered. Manual statements cannot provide that. Bank-sourced API data can.” – Clare, Finexer
For accounting and compliance platforms, the distinction between document-based and API-based data collection is covered in the accounting software security guide, which explains why secure financial records require bank-sourced data.
What Does Secure Bank Data Access Actually Require?
How Does Open Banking Change the Risk Profile?
| Data Access Method | Manual Bank Statements | Open Banking AIS |
|---|---|---|
| Data source | Client-submitted PDF or file | Direct from bank via regulated API |
| Tampering risk | High – PDF alterable before submission | None – data retrieved from bank at consent |
| Transmission security | Email or upload – no guaranteed encryption | TLS-encrypted API in transit |
| Data provenance | No chain of custody to issuing bank | Bank-authenticated, timestamped at retrieval |
| Audit trail | Upload record only – no source verification | Consent log per retrieval – timestamped, bank-verified |
| Credential exposure | Sometimes requires login credentials | No credentials shared – client authenticates with bank directly |
| Regulatory alignment | Depends on document handling procedures | UK GDPR compliant, PSR 2017 governed, FCA-authorised |
Open Banking AIS does not just speed up data collection. It changes how data security in financial services works at the collection step itself.
When a platform uses AIS to fetch bank statements or transaction data, the client authenticates directly with their bank. The platform never sees those credentials. The bank grants time-limited, scoped consent and transmits data via encrypted API.
The platform receives structured JSON – not a document, not a file, but data the bank produced and transmitted directly. There is no gap between the bank and the platform. No opportunity for alteration. No document to intercept in transit.
For solicitors and legal compliance teams addressing data security in financial services, the guide to fetching client bank statements for solicitors covers how Open Banking replaces manual collection in AML workflows.
Where Does This Matter Most for Regulated Platforms?
How Does Secure Data Access Apply Across Financial Workflows?
Data security in financial services is most exposed in regulated workflows – where the records collected form the basis of a legal or compliance decision. This is where it is ultimately tested: not in the storage layer, but in the evidence itself.
- AML and Source of Funds. A compliance team making an AML determination faces a direct data security challenge in financial services – the records it relies on may have been altered before submission. If those records can be altered before submission, the determination rests on potentially fraudulent data. Bank-sourced AIS data cannot have been tampered with between the bank and the platform.
- Income verification. An accounting SaaS verifying client income from uploaded payslips or emailed statements works from documents that may not reflect actual financial position. AIS data reflects real account activity at retrieval – not a curated client selection.
- Reconciliation. If source data powering reconciliation can be altered, the output cannot be fully trusted. This is a direct data security failure in financial services operations. Bank-verified transaction data removes the risk at the point of collection.
- Client onboarding. Regulated firms in property, insurance, or lending cannot demonstrate to a regulator that manually submitted evidence was unaltered. Consent logs and bank-authenticated data provide the audit trail that document uploads cannot.
How Does Finexer Support Secure Financial Data Access?

What Does Finexer’s AIS Provide for Data Security in Financial Services?
Finexer is not a document storage system, an encryption provider, or a security auditing tool.
Finexer provides FCA-authorised Open Banking AIS – the regulated infrastructure that allows UK platforms to access bank data directly, with consent, instead of relying on manually submitted statements.
- Direct bank data retrieval – transaction data from the bank at consent, not from client-submitted documents
- Tamper-proof by design – data comes from the bank via encrypted API, no document layer in between
- Timestamped access records – per-client audit trail for FCA and GDPR compliance documentation
- Structured JSON – consistent format across virtually every UK bank, no manual review required
- No credential exposure – clients authenticate with their bank directly
- Up to 7 years of transaction history, usage-based pricing, no setup fees, 3-5 weeks to production
Moving from manual statement collection to Open Banking AIS addresses the data integrity gap at the collection step – where data security in financial services most often fails.
The broader framework for financial data protection for UK platforms is covered in the financial data protection guide, which explains how consent flows and audit trails align with UK GDPR and FCA data security requirements.
“For compliance platforms, the question regulators ask is not whether data was stored securely – it is whether the data was authentic when it was collected. Open Banking AIS is the only method that provides a verifiable answer.” – Clare, Finexer
What I Feel
Financial platforms invest heavily in data security. In financial services, that investment almost always focuses on storage. The encryption works. The access controls hold.
But when the same platform asks a client to email a bank statement or upload a PDF, that investment in data security is irrelevant for that data point in financial services. The document may be genuine. It may not be. There is no way to tell.
This is not a theoretical vulnerability. It is the primary vector for financial document fraud – the exact gap that data security in financial services needs to close, and that Open Banking AIS was built to address.
Common Use Cases

Accounting SaaS
Manual statement uploads are where data security in financial services breaks first – introducing integrity risk directly into reconciliation workflows. Open Banking AIS retrieves transaction data directly from the bank – authenticated, timestamped, and unalterable. Reconciliation runs against verified data from day one.
Lawtech and Compliance Platforms
Source of Funds checks are where data security in financial services is most tested – evidence must withstand regulatory scrutiny. Bank-authenticated data provides the audit trail that manually submitted statements cannot – demonstrating to regulators that evidence was unaltered.
Fintech Products
Platforms making lending or affordability decisions face a core data security challenge in financial services: the provenance of the financial records they rely on cannot be verified when those records arrive as client-submitted documents. Bank-sourced transaction data carries verifiable provenance from bank to platform – the standard required for any regulated financial decision.
Financial Operations Tools
Data security in financial services operations begins with what feeds the reconciliation layer. Finance ops teams that currently fetch bank statements manually for period-end close can replace that step with structured, real-time bank data – removing both the security risk and the operational overhead.
Is data security an FCA rule in the UK?
Yes. The FCA requires regulated firms to maintain secure systems and controls for customer data under SYSC 8 and the FCA Handbook. This includes data integrity, access controls, and breach notification. Under UK GDPR, firms must report personal data breaches within 72 hours. Open Banking AIS access also falls under Payment Services Regulations 2017.
How do you fetch bank statements securely for compliance workflows?
Secure bank statement retrieval uses Open Banking AIS to access transaction data directly from the client’s bank with their consent. No credentials are shared with the platform. Data travels bank-to-platform via encrypted API with a consent log per retrieval – providing bank-authenticated, timestamped records that replace manually submitted PDFs.
Can you get 7 years of bank statements via Open Banking?
Transaction history depth via Open Banking AIS varies by bank. Finexer provides up to 7 years of transaction history where the bank supports it. Standard Open Banking typically covers 12-24 months. For workflows requiring extended history – insolvency, Source of Funds, long-term income verification – history depth is configured during integration setup.
What regulations apply to financial data access in the UK?
UK platforms must comply with UK GDPR, the Data Protection Act 2018, and Payment Services Regulations 2017. The Data (Use and Access) Act 2025 updates data sharing obligations. FCA-authorised AIS providers must meet the PRA’s PS7/26 operational resilience framework (March 2026). Consent logs per retrieval form part of a platform’s GDPR compliance documentation.
Move from document risk to bank-verified data with Finexer’s FCA-authorised Open Banking AIS

